How to Build a Third-Party Risk Management Program from Scratch
Most companies realize they need a vendor risk management process only after something goes wrong. A vendor gets breached. An audit uncovers gaps. A regulator asks questions you cannot answer.
You do not have to wait for that moment. Here is how to build a solid TPRM program from the ground up.
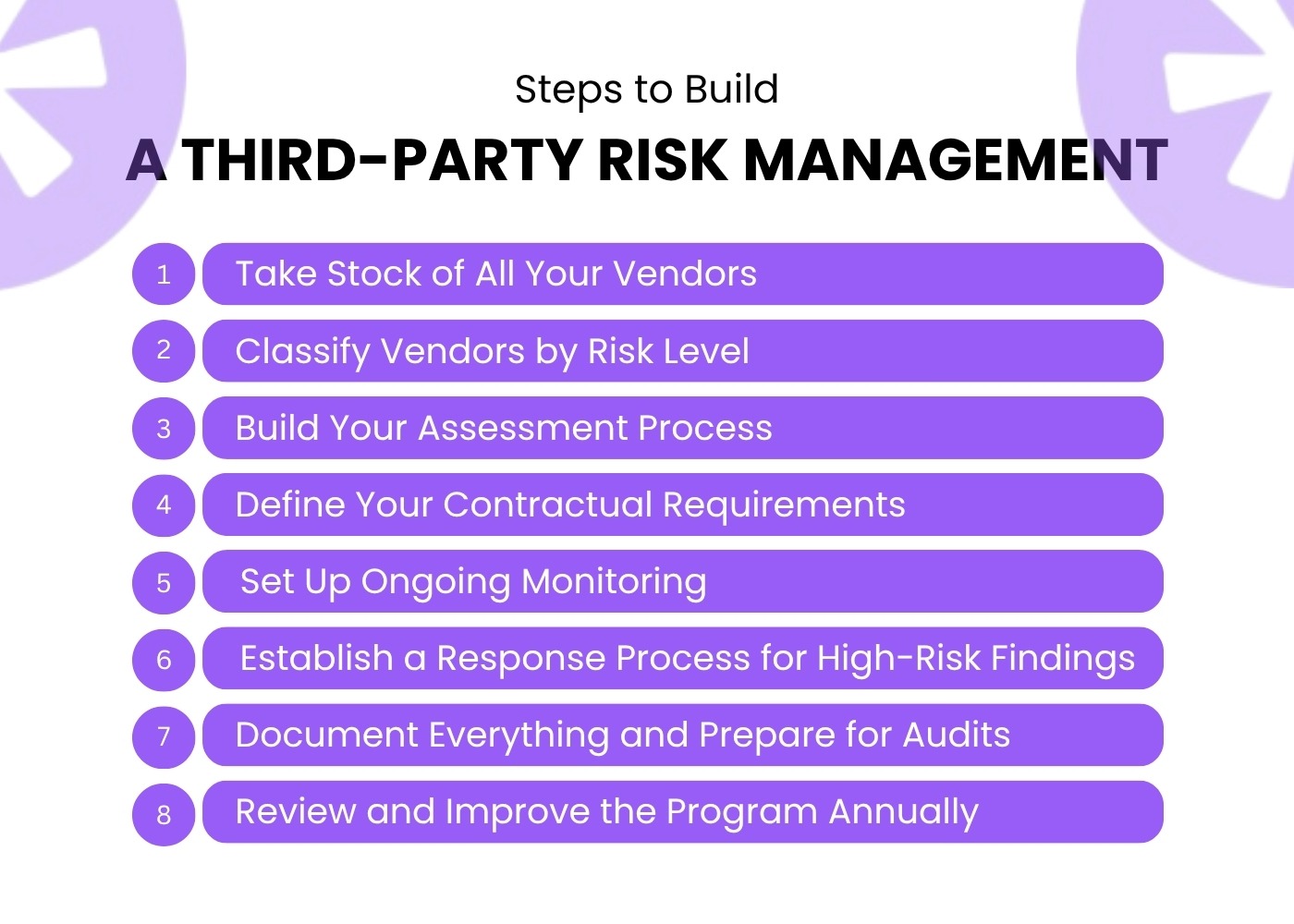
Step 1: Take Stock of All Your Vendors
Start with a complete vendor inventory. List every third party that has access to your systems, data, or operations. Include software vendors, cloud providers, payroll processors, marketing platforms, and any subcontractors they use.
Most organizations are surprised by how many vendors they actually have. Group them roughly by:
- What data can they access
- What systems do they connect to
- How critical they are to your operations
Step 2: Classify Vendors by Risk Level
Not every vendor deserves the same level of scrutiny. A vendor who stores sensitive customer financial data is far riskier than one who prints your office stationery.
Build a simple risk tiering model:
- Tier 1 (Critical): Access to sensitive personal data, financial data, or core infrastructure
- Tier 2 (Moderate): Limited data access, non-critical services
- Tier 3 (Low): No data access, commodity services
Your third-party risk management framework should then dictate how deeply you assess each tier.
Step 3: Build Your Assessment Process
For each vendor tier, define what you need to know before onboarding and periodically after. A standard vendor risk program uses security questionnaires, document reviews, and sometimes on-site or virtual audits.
A Tier 1 vendor assessment might cover:
- Data handling and storage practices
- Encryption standards
- Incident response procedures
- Sub-processor disclosures
- Compliance certifications like SOC 2 or ISO 27001
Tier 3 vendors may only need basic due diligence documentation.
Step 4: Define Your Contractual Requirements
Every vendor relationship should have clear contractual language covering data protection obligations. Under regulations like DPDP, GDPR, and CCPA, you remain responsible for what your vendors do with the data you share. Contracts should address:
- Data processing limitations
- Breach notification timelines
- Right to audit clauses
- Subprocessor approval requirements
- Data deletion and return upon termination
Learn more about embedding accountability into vendor contracts in this guide on third-party contract management.
Step 5: Set Up Ongoing Monitoring
Onboarding assessment is just the start. A real TPRM program includes continuous monitoring of your vendor landscape.
Ongoing monitoring should watch for:
- Security incidents or breaches at vendor organizations
- Changes in vendor ownership or subcontractors
- Compliance certification lapses
- News alerts related to vendor security posture
Without monitoring, your program is only as good as your last questionnaire, which may be months out of date.
Step 6: Establish a Response Process for High-Risk Findings
When a vendor fails an assessment or triggers a risk alert, your team needs a clear playbook. Define in advance:
- Who gets notified
- What remediation steps are required
- What the timeline for resolution looks like
- When a vendor relationship should be terminated
This avoids scrambling and inconsistent responses when something actually happens.
Step 7: Document Everything and Prepare for Audits
Regulators and auditors want evidence, not promises. Keep records of every vendor assessment, questionnaire response, remediation action, and contract update. Your audit and reporting capability should make it easy to pull this evidence quickly.
Build your documentation habits from day one so audit preparation is never a last-minute scramble.
Step 8: Review and Improve the Program Annually
A TPRM program is not a one-time build. Regulations evolve. Your vendor landscape changes. New risks emerge. Review your framework at least once a year and update your questionnaires, risk tiers, and monitoring criteria accordingly.
Read about common vendor risk management challenges to understand what to watch for as your program matures.
Conclusion
Building a third-party risk management framework is not complicated, but it does require consistency. Start simple, get the foundations right, and automate as you scale.
Redacto's vendor risk management platform helps compliance teams run assessments, monitor vendors continuously, and generate audit-ready reports, all in one place. Contact us to learn more, or drop us a message on WhatsApp.
How to Build a Third-Party Risk Management Program from Scratch
Most companies realize they need a vendor risk management process only after something goes wrong. A vendor gets breached. An audit uncovers gaps. A regulator asks questions you cannot answer.
You do not have to wait for that moment. Here is how to build a solid TPRM program from the ground up.
Step 1: Take Stock of All Your Vendors
Start with a complete vendor inventory. List every third party that has access to your systems, data, or operations. Include software vendors, cloud providers, payroll processors, marketing platforms, and any subcontractors they use.
Most organizations are surprised by how many vendors they actually have. Group them roughly by:
- What data can they access
- What systems do they connect to
- How critical they are to your operations
Step 2: Classify Vendors by Risk Level
Not every vendor deserves the same level of scrutiny. A vendor who stores sensitive customer financial data is far riskier than one who prints your office stationery.
Build a simple risk tiering model:
- Tier 1 (Critical): Access to sensitive personal data, financial data, or core infrastructure
- Tier 2 (Moderate): Limited data access, non-critical services
- Tier 3 (Low): No data access, commodity services
Your third-party risk management framework should then dictate how deeply you assess each tier.
Step 3: Build Your Assessment Process
For each vendor tier, define what you need to know before onboarding and periodically after. A standard vendor risk program uses security questionnaires, document reviews, and sometimes on-site or virtual audits.
A Tier 1 vendor assessment might cover:
- Data handling and storage practices
- Encryption standards
- Incident response procedures
- Sub-processor disclosures
- Compliance certifications like SOC 2 or ISO 27001
Tier 3 vendors may only need basic due diligence documentation.
Step 4: Define Your Contractual Requirements
Every vendor relationship should have clear contractual language covering data protection obligations. Under regulations like DPDP, GDPR, and CCPA, you remain responsible for what your vendors do with the data you share. Contracts should address:
- Data processing limitations
- Breach notification timelines
- Right to audit clauses
- Subprocessor approval requirements
- Data deletion and return upon termination
Learn more about embedding accountability into vendor contracts in this guide on third-party contract management.
Step 5: Set Up Ongoing Monitoring
Onboarding assessment is just the start. A real TPRM program includes continuous monitoring of your vendor landscape.
Ongoing monitoring should watch for:
- Security incidents or breaches at vendor organizations
- Changes in vendor ownership or subcontractors
- Compliance certification lapses
- News alerts related to vendor security posture
Without monitoring, your program is only as good as your last questionnaire, which may be months out of date.
Step 6: Establish a Response Process for High-Risk Findings
When a vendor fails an assessment or triggers a risk alert, your team needs a clear playbook. Define in advance:
- Who gets notified
- What remediation steps are required
- What the timeline for resolution looks like
- When a vendor relationship should be terminated
This avoids scrambling and inconsistent responses when something actually happens.
Step 7: Document Everything and Prepare for Audits
Regulators and auditors want evidence, not promises. Keep records of every vendor assessment, questionnaire response, remediation action, and contract update. Your audit and reporting capability should make it easy to pull this evidence quickly.
Build your documentation habits from day one so audit preparation is never a last-minute scramble.
Step 8: Review and Improve the Program Annually
A TPRM program is not a one-time build. Regulations evolve. Your vendor landscape changes. New risks emerge. Review your framework at least once a year and update your questionnaires, risk tiers, and monitoring criteria accordingly.
Read about common vendor risk management challenges to understand what to watch for as your program matures.
Conclusion
Building a third-party risk management framework is not complicated, but it does require consistency. Start simple, get the foundations right, and automate as you scale.
Redacto's vendor risk management platform helps compliance teams run assessments, monitor vendors continuously, and generate audit-ready reports, all in one place. Contact us to learn more, or drop us a message on WhatsApp.
Frequently asked questions
A TPRM (Third-Party Risk Management) program is a structured process for identifying, assessing, and managing risks that come from working with external vendors and partners.
Focus deep assessments on vendors with access to sensitive data or critical systems. Low-risk vendors may only need basic due diligence.
Yes. Third-party risk management software can automate questionnaire distribution, risk scoring, and continuous monitoring significantly.
Start by listing all your vendors and categorizing them by the level of data access and operational criticality they have.
Under India's DPDP Act, organizations must ensure that their data processors (vendors) handle personal data according to the law. Contracts and oversight processes are required.
Tier 1 vendors should be reassessed at least annually, or sooner if major changes occur. Tier 2 and 3 vendors can follow longer cycles.
Contact Us




%20Redacto%20logo_New.png)


.jpg)
.jpg)
.webp)
